The Organization’s security program ensures compliance with a multitude of industry standards, regulations, and best practices through a single framework, based upon the Unified Compliance Framework (UCF), by aggregating authoritative sources into a collective whole. This framework then aligns and harmonizes the mandates within a de-duplicated list of common controls.
Internal Policies
As part of the Security Governance Framework, the Security team has adopted common definitions for policies and associated documentation. This hierarchy guides the structure of these documents to ensure consistent application throughout the Organization.
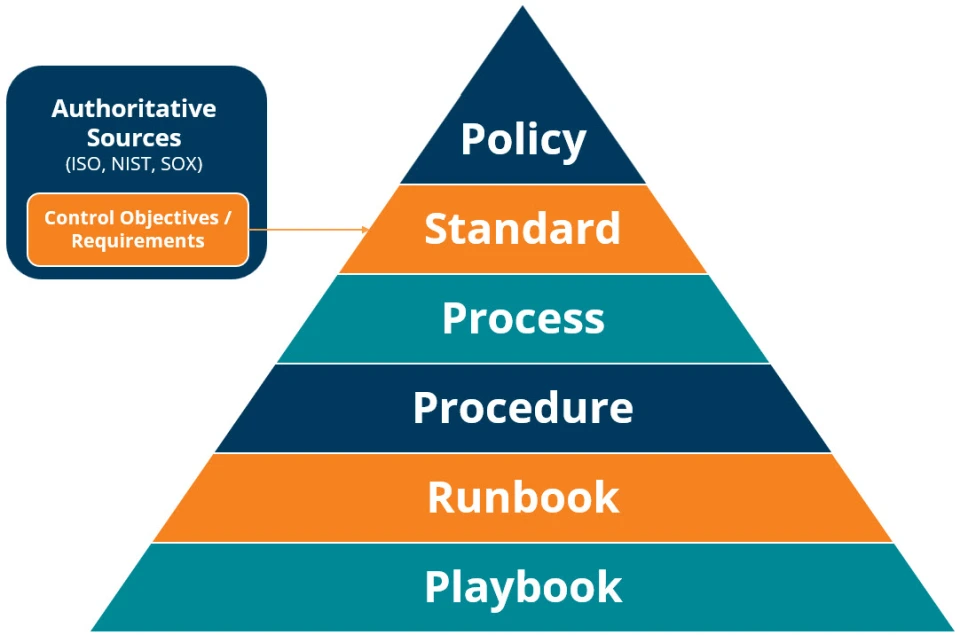
| Authoritative Sources EXAMPLE: ISO or NIST | – Guidance, standards, requirements, and best practices to ensure confidentiality, integrity, and availability of information – Shape and maintain effective information security practices |
| Control Objectives EXAMPLE: Ensure confidentiality, integrity, and availability of personal data | – Specifications defined by authoritative sources to satisfy control objectives and ensure protection of information, systems, and assets – Address potential risks and safeguard sensitive information and systems |
| Policy EXAMPLE: Zayo Security Policy | What and why must this be done? – Defines the rules, intent, and expectations of the Organization to guide decision making and operations – Long-term focus with routine reviews, but remain fairly static – Shaped by leading governance practices, laws, regulations, and industry standards |
| Standard EXAMPLE: Technical Security Standard | What does “good” look like? – Defines specific, measurable requirements – Updated more frequently than policy and span multiple topic areas – Testable criteria – Removes ambiguity and supports policy |
| Process EXAMPLE: System Backup Process | How does work flow across roles? – Describes workflows and responsibilities – Includes inputs and outputs – Cross-functional |
| Procedure EXAMPLE: Submitting an Exception Request | How exactly is this task performed? – Step-by-step execution instructions – System / tool-specific – Repeatable |
| Runbook EXAMPLE: Restarting a Server | How do we handle known operational events? – Handles routine operational tasks – Action-based, predictable scenarios – Often repeatable |
| Playbook EXAMPLE: Malware Detection Response | How do we respond when something goes wrong? – Guides response to incidents or scenarios – Decision trees, roles, communication, escalation paths |
Zayo does not share internal governance documents in their entirety as they are treated as internal resources that are proprietary in nature. This fosters accountability and confidentiality, guiding teams through crises while ensuring compliance with industry standards. This approach underscores Zayo’s commitment to resilience and security. Tables of contents are available for download:
Security Governance Framework
Zayo Security Policy
Acquisition or Sale of Facilities, Technology, and Services Standard
Audits and Risk Management Standard
Harmonization Methods and Manual of Style Standard
Human Resources Management Standard
Leadership and High Level Objectives Standard
Monitoring and Measurement Standard
Operational and Systems Continuity Standard
Operational Management Standard
Physical and Environmental Protection Standard
Privacy Protection for Information and Data Standard
Records Management Standard
Systems Design, Build and Implementation Standard
Systems Hardening Through Configuration Management Standard
Technical Security Standard
Third Party and Supply Chain Oversight Standard
External Policies
Zayo is dedicated to conducting business with the highest level of integrity and responsibility. We believe that ethical practices and compliance with all relevant laws and regulations are fundamental to building trust and ensuring the long-term success of our relationships with customers, partners, and stakeholders.
We are committed to maintaining transparency, fairness, and accountability in all our business dealings, adhering to the highest ethical standards and continuously monitoring our operations to ensure compliance with applicable laws and industry regulations. Our external policies are available to all under the Governance category of Trust Center.