Does Zayo have network access control policies and procedures in place for your information systems that are aligned with industry standards or control frameworks?
Yes. Zayo’s security program is based upon the Unified Compliance Framework (UCF) and structured around a set of control objective categories addressing controls from a multitude of authoritative industry standards and requirements. For more information about the UCF, refer to https://www.unifiedcompliance.com/home.
What are Zayo practices for items such as federation, privileged users, and role-based access control for end-user devices?
Access controls include role-based access controls (RBAC), Single Sign On (SSO), and Identity Access Management.
How does Zayo ensure remote access is managed for end-user devices or employees and suppliers, including deactivation of accounts? (e.g. Multi-factor authorization, encryption, protection from malware, etc.)
Remote access is managed using MFA, local disk encryption, VPN and ZIA internet protection, and malware protection.
Is cybersecurity training required for personnel who have administrative rights to your enterprise computing resources?
Yes.
What is the frequency for verifying personnel training compliance?
Training compliance takes place upon hire and on an annual basis.
What cybersecurity training is required for your third-party stakeholders (e.g., suppliers, customers, partners, etc.) who have network access?
Vendor workers and contractors are required to complete Organizational security training, which is administered, monitored, and tracked. Suppliers are responsible for their own security training programs.
Does Zayo include contractual obligations to protect information and information systems handled by your suppliers?
Yes.
What standard cybersecurity standards or frameworks are the contractual supplier terms for information protection aligned to, if any?
Agreements with Suppliers must include, based on the need, the requirements to address the information security risks associated with information and communications technology services. Based on the security requirements agreed upon when signing the Supplier contract, the Organization reserves the right to conduct formal and regular reviews of the adherence to the specified requirements, which can include Supplier review and product validation.
Do you have an organizational policy on the use of encryption that conforms with industry standards or control frameworks?
Yes.
Are incident detection and reporting practices defined and documented which outline the actions that should be taken in the case of an information security or cybersecurity event?
Yes. The Security Information and Event Management (SIEM) system detects anomalous and malicious activity in the Zayo environment by correlating logs and events across the Zayo network. This tool help provide real-time analysis to the Security Operations Center (SOC) to identify patterns that indicate potential security breaches such as unusual access patterns, failed login attempts or data exfiltration. Zayo collects logs focused on security related activities and source owner audit purposes. Logs are retained for 365 days and are under continuous review. Alerts are automated as logs are tested against system rules, and actionable events are addressed by the SOC.
What industry standards or controls frameworks are followed for encryption and key management?
Zayo’s security program is based upon the Unified Compliance Framework (UCF) and structured around a set of control objective categories addressing controls from a multitude of authoritative industry standards and requirements. For more information about the UCF, refer to https://www.unifiedcompliance.com/home.
Does Zayo have hardening standards in place for network devices (e.g., wireless access points, firewalls, etc.)?
Yes.
What protections exist to provide network segregation where appropriate (e.g., intrusion detection systems)?
Customer and Corporate Production, Telemetry (monitoring), and Business systems are segmented and isolated from one another.
What controls exist to continuously monitor changes to your network architecture?
Zayo’s security program is based upon the Unified Compliance Framework (UCF) and structured around a set of control objective categories addressing controls from a multitude of authoritative industry standards and requirements. For more information about the UCF, refer to https://www.unifiedcompliance.com/home.
How does Zayo manage prioritization and mitigation of threats discovered on your networks?
Security Operations is active 24/7. Multiple endpoint detection and response tools are in place providing detection, enterprise logging and compromise indicators of vulnerability. Notifications of incidents creates response tasks that are tracked and managed.
How does Zayo track changes to software versions on your servers?
Changes are tracked using reports from our scanning agents.
How does Zayo convey cloud security requirements to your suppliers/sub-contractors?
Requirements are agreed upon through contractual language and Data Processing Addendums.
Does Zayo run automated scans to detect vulnerabilities?
Multiple endpoint detection and response tools are in place providing detection, enterprise logging and compromise indicators of vulnerability. Notifications of incidents creates response tasks tracked and managed and responded to by the Security Operations Center (SOC).
How does Zayo obtain information about vulnerabilities?
Threat hunting, machine learning, and threat intelligence is used.
Does Zayo you configure and refresh systems/endpoints using a standard image build?
A defined standard build exists and is enforced as appropriate.
How does Zayo manage critical patches?
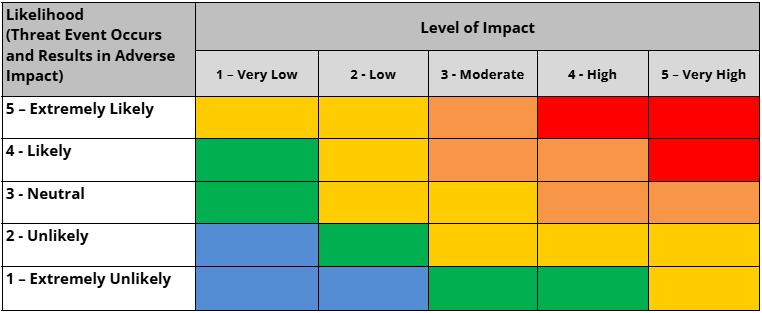
Per policy, based on severity ratings, the patch policy priority schedule is as follows:
- Critical: Review within seven (7) business days with deployment based on review
- High: Review within 30 days with deployment based on review
- Medium: Review within 90 days with deployment based on review
- Low: 180 days
Are there policies and procedures in place to ensure that the environment providing service to customers is not capable of being accessed from or reliant upon equipment present within a Restricted Country?
Zayo allows access from those locations/countries where our employees, contractors, and vendors are located. Zayo’s Threat Intelligence infrastructure will always block specific sources of high risk or active threats, regardless of location. Zayo determines high risk countries based on the following criteria:
The following high risk countries are not permitted for inbound traffic:
- China
- Cuba
- Iran
- Iraq
- North Korea
- Russia/Ukraine
Does Zayo engage a third party for external penetration testing on your physical properties?
No external penetration testing is conducted on physical properties.
Does Zayo perform inspections for physical tampering or alteration of hardware components within the system?
Yes, inspections are performed for physical tampering on some systems.
Does Zayo have protective monitoring (e.g. SOC services) enabled for all remote assets?
Proactive monitoring is in place for all endpoints using advanced tooling; protective monitoring and response enabled to manage incidents such as network access control (NAC), privileged access management (PAM), managed detection and response (MDR), and data loss prevention (DLP).
Does Zayo engage a third party for external penetration testing on your network?
Yes, although much of our penetration testing is done internally. The following tests are performed internally on a regular cadence to identify potential vulnerabilities and assess the Organization’s security posture:
- Network penetration testing
- Web application penetration testing
- Mobile application penetration testing
A third party is engaged for external penetration testing on our network on an ad hoc basis.
Does Zayo have documented policies or procedures for identification and detection of cyber threats?
Yes.
What processes does Zayo have in place to promptly detect cyber threats?
Multiple endpoint detection and response tools are in place providing detection, enterprise logging, and compromise indicators of vulnerability.
Does Zayo have defined and documented incident detection practices that outline which actions should be taken in the case of an information security or cybersecurity event?
Yes.
Are cybersecurity events centrally logged, tracked, and continuously monitored?
Yes. The Security Information and Event Management (SIEM) system detects anomalous and malicious activity in the Zayo environment by correlating logs and events across the Zayo network. This tool help provide real-time analysis to the Security Operations Center (SOC) to identify patterns that indicate potential security breaches such as unusual access patterns, failed login attempts or data exfiltration. Zayo collects logs focused on security related activities and source owner audit purposes. Logs are retained for 365 days and are under continuous review. Alerts are automated as logs are tested against system rules, and actionable events are addressed by the SOC.
Are incident detection practices continuously improved?
Yes.
Does Zayo require vulnerability scanning of software running within the enterprise prior to acceptance?
Yes.
What procedures or policies exist, if any, for detecting vulnerabilities in externally obtained software (such as penetration testing of enterprise and non-enterprise software)?
Architecture reviews/acceptance criteria, vulnerability scans, and penetration testing.
Does Zayo manage updates, version tracking of new releases, and patches (including patching history) for your software and software services offerings?
Yes.
Does Zayo deploy anti-malware software?
Yes.
How does Zayo manage the identification of threats within your supply chain, including suppliers and sub-contractors?
Suppliers must immediately report any security or other event that creates reasonable suspicion that there may be a violation of the above requirements and take appropriate steps to immediately address any security incident and cooperate with the Organization in respect to the investigation of such incident.
What processes are in place to act upon external credible cyber security threat information received?
Security Operations is active 24/7. Multiple endpoint detection and response tools are in place providing detection, enterprise logging and compromise indicators of vulnerability. Notifications of incidents automatically create response tasks that are tracked and managed.
Does Zayo address the interaction of cybersecurity operational elements (e.g., SOC, CSIRT, etc.) with the physical security operational elements protecting the organization’s physical assets?
Yes.
How does Zayo ensure that physical security incidents and suspicious events are escalated to cybersecurity operations staff?
Incident response for both physical security and cyber security are managed by Security Operations.
Are cybersecurity vulnerabilities for industrial control systems, including physical access controls and video monitoring systems, tracked?
Yes.
What standards or frameworks are followed for management of IT and OT system interactions?
Zayo’s security program is based upon the Unified Compliance Framework (UCF) and structured around a set of control objective categories addressing controls from a multitude of authoritative industry standards and requirements. For more information about the UCF, refer to https://www.unifiedcompliance.com/home.
Does Zayo have a policy or procedure for the handling of information that is consistent with its classification?
Yes.
What is Zayo’s process to verify that information is classified according to legal, regulatory, or internal sensitivity requirements?
We have adopted a zero-trust control and principles of least privilege.
How does Zayo convey requirements for data retention, destruction, and encryption to your suppliers?
Through contractual language and Data Processing Addendums.
Does Zayo have documented policies or procedures for internal identification and management of vulnerabilities within your networks and enterprise systems?
Yes.
What industry standards or frameworks are followed for vulnerability management?
Zayo’s security program is based upon the Unified Compliance Framework (UCF) and structured around a set of control objective categories addressing controls from a multitude of authoritative industry standards and requirements. For more information about the UCF, refer to https://www.unifiedcompliance.com/home.
How does Zayo identify vulnerabilities in your supply chain (suppliers/subcontractors) before they pose a risk to your organization?
The Supplier must immediately report any security or other event that creates reasonable suspicion that there may be a violation of the above requirements and take appropriate steps to immediately address any security incident and cooperate with the Organization in respect to the investigation of such incident.
How does Zayo assess and prioritize the mitigation of vulnerabilities discovered on your internal networks and systems?
Upon discovery, Security Operations creates an incident ticket for remediation.